Energy and utility facilities face threats ranging from opportunistic criminals to coordinated attacks. Protecting these critical infrastructure assets requires compliance with federal regulations designed to safeguard the nation’s power and water systems. Noncompliance exposes organizations to financial penalties, operational shutdowns, and lasting reputational damage. With regulators intensifying oversight and criminal threats escalating, understanding applicable regulations and implementing compliant security measures is essential.
Security Regulations for Energy and Utilities
Multiple federal agencies influence security compliance for energy and utilities. Key frameworks governing physical security for energy and utilities facilities include:
- NERC CIP-014-3: The North American Electric Reliability Corporation (NERC) requires that transmission owners conduct risk assessments, identify critical facilities vulnerable to physical attacks, and implement protective measures to prevent instability or cascading failures across the electrical grid.
- FERC enforcement: The Federal Energy Regulatory Commission (FERC) oversees and enforces NERC standards, and can impose penalties costing millions of dollars for noncompliance with physical and cybersecurity requirements.
- EPA AWIA: The Environmental Protection Agency’s America’s Water Infrastructure Act (AWIA) requires water utilities serving over 3,300 people to conduct risk and resilience assessments and develop emergency response plans addressing physical threats to critical assets.
Why Energy and Utilities Security Compliance Matters
Regulatory requirements exist to help energy and utility companies protect themselves and the grid from escalating threats. For example, 2024 saw 220 physical security intrusions at Western Interconnection energy facilities alone, which was more than double the previous year’s incidents. Beyond the immediate financial loss from stolen or damaged equipment, the consequences of inadequate security include:
- Regulatory penalties: Fines for noncompliance can cost hundreds of thousands, or more. For example, FERC imposed a $350,000 penalty on the Los Angeles Department of Water and Power in 2025 for inaccurate compliance reporting.
- Operational disruption: Physical attacks on energy infrastructure can cause cascading failures affecting thousands of customers and requiring weeks or months of repair work.
- Reputational damage: Security failures erode stakeholder confidence, impacting long-term financial prospects and potentially triggering additional regulatory scrutiny.
Common Utilities Compliance Failures to Avoid
Understanding the most common causes of compliance errors can help you plan to keep your facility in line with regulations. Here are four common errors and how to avoid them.
Incomplete Risk Assessments
Facilities often treat risk assessments as one-time exercises rather than living documents. Common errors include failing to reassess risks when adding new equipment or infrastructure, omitting required physical security sections from assessments, and treating initial evaluations as final rather than updating them as threats evolve. For example, utilities often submit incomplete AWIA risk assessments with critical sections missing.
Avoid this by scheduling formal reassessments aligned with regulatory cycles, documenting all facility changes affecting risk profiles, and ensuring assessments address both physical and cybersecurity threats.
Poor Vendor Oversight
While facilities increasingly outsource security system maintenance, compliance responsibility cannot be transferred to third parties. Auditors frequently discover gaps where vendors handle firewall management, access control testing, or vulnerability assessments without proper oversight or documentation. Then, when regulators request evidence, facilities cannot produce records proving the required work was completed.
Partnering with a security provider with a dedicated compliance team will ensure you receive all necessary documentation to show compliant installations and maintenance.
Physical Access Documentation Gaps
Regulators require detailed records proving that only authorized personnel can access critical areas. Common violations include incomplete entry monitoring logs, missing visitor escort documentation, and outdated access permissions that weren’t revoked when employees left.
Maintain timestamped logs for all entry points, document visitor procedures, and conduct regular reviews removing former personnel from access lists. Modern access control systems automate access logging to simplify compliance.
Missing Software Baselines and Asset Inventories
Facilities moving security functions to cloud-based platforms often fail to document what software is running on their systems, how they verify it hasn’t been tampered with, and how they assess vulnerabilities. Regulators expect facilities to maintain records showing exactly what security technology they use and how they ensure it remains secure. Without this documentation, facilities cannot prove their security controls actually work during audits.
Keep detailed inventories of all security system components, establish processes for verifying software integrity, and confirm cloud service providers can help you meet documentation requirements before signing contracts.
How to Implement Compliant Physical Security Systems
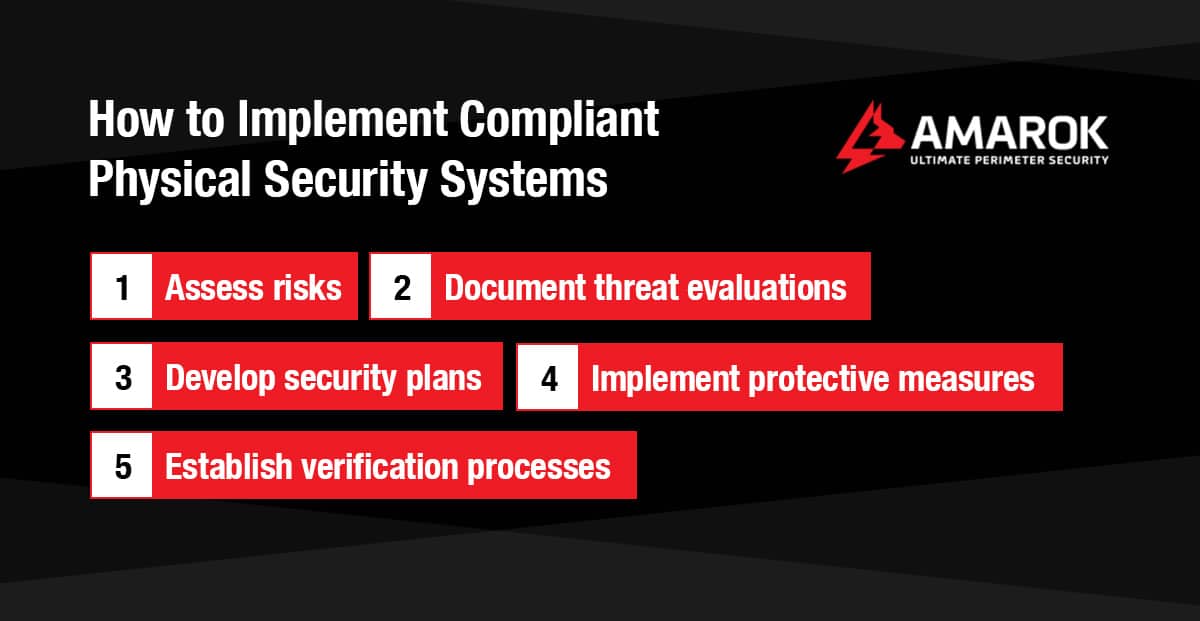
Compliance regulations require facilities to connect every security decision to resolving documented vulnerabilities. Whether you’re addressing NERC transmission protection standards or EPA AWIA resilience assessments, the process involves identifying critical infrastructure, assessing site-specific threats, and implementing protective measures to mitigate documented risks. Follow these steps to develop your compliance strategy:
- Assess risks: Professional security risk assessments identify property-specific vulnerabilities, analyze local crime data, and evaluate how site layout and access patterns affect risk levels. Document transmission analyses identifying critical facilities per CIP-014 criteria, including potential cascading failure scenarios and coordinated attack vulnerabilities from nearby access points.
- Document threat evaluations: Create formal threat assessment documents for critical facilities, considering factors like proximity to roads, line of sight between multiple locations, and local threat intelligence.
- Develop security plans: Based on your risk and threat assessments, create documented plans specifying protective measures for each critical facility, organized around deterrence, detection, and delay.
- Implement protective measures: Deploy security solutions that address identified vulnerabilities and satisfy your documented security plans.
- Establish verification processes: Create procedures for regular security plan reviews, testing of detection systems, and documentation of all security-related activities to demonstrate ongoing compliance.
Most effective energy and utilities security systems include three protective layers:
- Deterrence: Perimeter fencing, signage, and visible security measures reduce opportunistic attacks and address vulnerabilities criminals could exploit to gain access.
- Detection: Monitoring systems identify intrusions or suspicious behavior, satisfy surveillance requirements, and can create timestamped event records for audit trails.
- Delay: Access controls and physical barriers slow would-be intruders down, providing time for law enforcement response while documenting the security program’s effectiveness.
This layered approach is the most effective way to address documented vulnerabilities, prevent crime, and demonstrate compliance.
Protect Your Facility With Compliant Perimeter Security Solutions by AMAROK
For the energy and utilities industries, security compliance requires thorough risk assessment and tailored protective measures. With AMAROK, you gain access to compliance and security experts with proven perimeter security solutions.
AMAROK is a trusted provider of energy and utility security technology. Our solutions, from The Electric Guard Dog™ Fence to monitored video surveillance, support compliant security programs and prevent 99% of external theft for over 8,000 sites nationwide. After a threat assessment to understand your site’s vulnerabilities, our security experts will work with you to create a custom perimeter security system while our dedicated government relations and compliance team ensures your system aligns with all applicable regulations and permitting requirements.
Connect with your nearest AMAROK expert for a free threat assessment today.